Trezor Login: Secure Access to Your Crypto Assets
Learn how to safely log in to your Trezor hardware wallet and manage your cryptocurrencies confidently.
Why Proper Trezor Login Matters
Logging into your Trezor wallet is more than just a step—it’s the gateway to controlling your crypto assets securely. Using Trezor Login correctly ensures that your private keys remain safe and reduces the risk of phishing or unauthorized access.
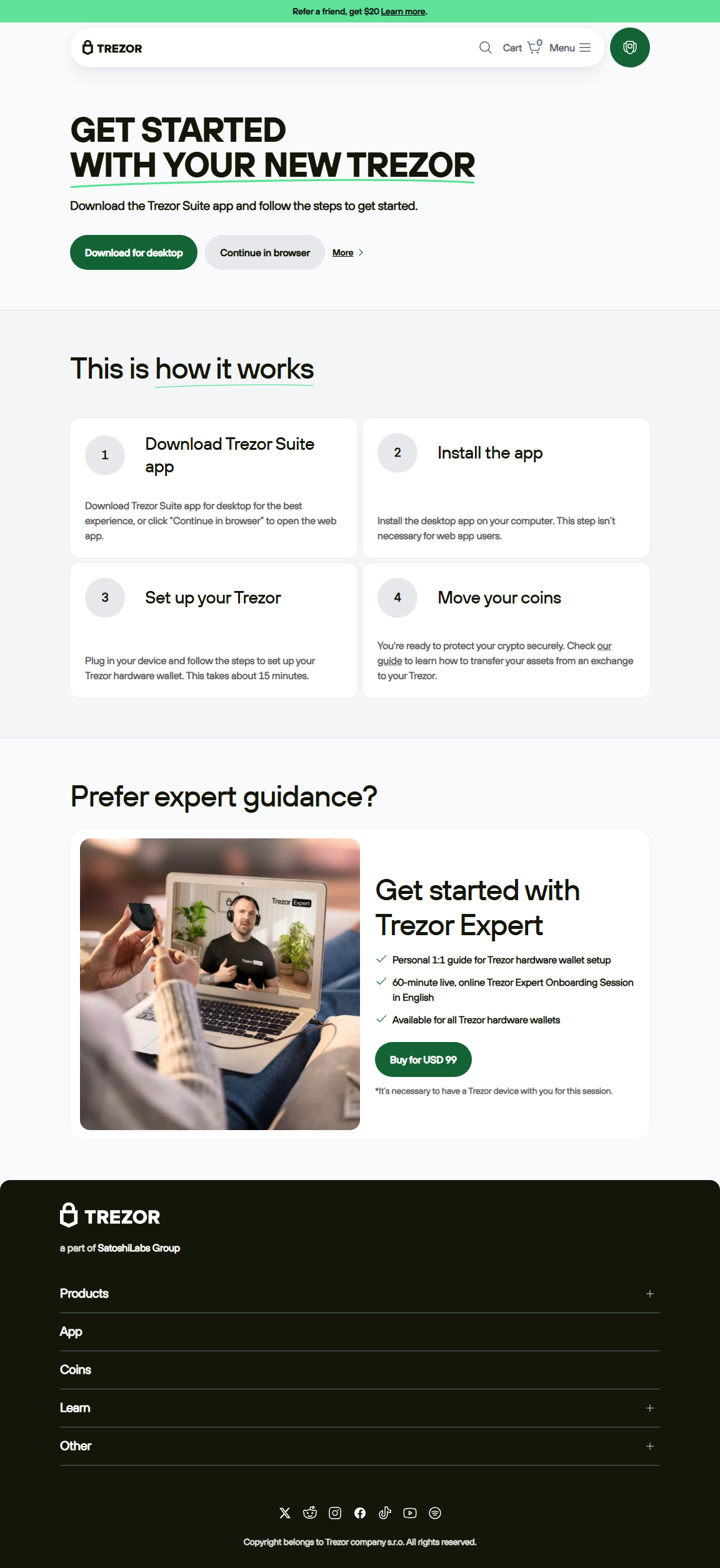
Step-by-Step Guide to Trezor Login
Step 1: Open Trezor Suite or Visit Trezor Login Page
Ensure you are using the official site or Trezor Suite application. Avoid clicking links from emails or messages that could be phishing attempts.
Step 2: Connect Your Trezor Device
Plug your Trezor device into your computer. Wait for the device to initialize and confirm the connection with Trezor Suite or the login portal.
Step 3: Enter Your PIN
Use the Trezor device to enter your PIN securely. Never type your PIN on untrusted devices or websites.
Step 4: Access Your Accounts
Once logged in, you can view balances, manage multiple crypto accounts, send or receive assets, and stake supported cryptocurrencies securely.
Security Best Practices for Trezor Login
- Always use the official Trezor login page or Trezor Suite.
- Never share your PIN or recovery seed phrase with anyone.
- Ensure your computer or device is malware-free before connecting.
- Regularly update firmware and Trezor Suite for security improvements.
- Consider enabling passphrase protection for an extra layer of security.
Trezor Login vs Hot Wallets
| Feature | Trezor Login | Hot Wallet | Exchange Wallet |
|---|---|---|---|
| Security | Offline keys + PIN | Online only | Exchange-controlled |
| Recovery | Seed phrase | Password only | Exchange-managed |
| Best Use | Secure long-term storage | Small, frequent transactions | Active trading |
FAQs About Trezor Login
Yes, but ensure each device is secure and has Trezor Suite or official login access.
You can restore access using your recovery seed phrase on a new Trezor device.
Yes, because private keys remain offline, reducing exposure to hacks and malware.
Conclusion
Trezor Login is the secure gateway to managing your crypto assets. By following best practices and using official software, you ensure the safety and control of your digital portfolio.